In this post, We will be dicussing how to setup Federated SAML based Authentication in Salesforce.
SAML stands for “Security Assertion Markup Language” and it is Open standard for exchanging Authentication and Authorization between Systems. SAML based authentication is supported by all editions of Salesforce.
User Validation can be initiated by any one of below two types:
- Service Provider Initiated SSO
- Identity Provider (IDp) initioated SSO
We are going to use Identity Provider Initiated SSO in this article. Means User will Login from Outside(IDp) and will be redirected to Salesforce (Service Provider). Identity Provider must follow Federated Authentication (SAML) standard which should be deployed to DMZ (URL should be publicly accessible on Internet) layer of your Organization. As a Salesforce developer you should assume that you will always get IDp URL which implements SSO and implements valid SAML response. To Quickly start with this tutorial assume that your organization already deployed SAML based Authentication endpoint and for that we will be using great Heroku app available freely as open source named “AXIOM“.
AXIOM is java based heroku application which implements SAML and can be used for testing purpose to check whether SSO is working properly or not.
IDp Initiated Single Sign On :
In IDp Initiated SSO, User Directly logins to Identity provider and IDp redirects user to proper Salesforce Instance with SAML assertion in request (Service Provider). If SAML assertion is valid then Salesforce validates that user successfuly.

Step 1 : Enable My Domain
First step is to enable “My Domain” in Salesforce. This functionality will provide a unique name to your salesforce Instance. It may take 24 hours to activate. Your Domain name must be unique and not used by someone else.
Step 2: Download Identity Provider Certificate
In this step we are going to get certificate from IDp. This certificate will be used by Salesforec to validate that client coming for user authentication is valid to avoid any unauthorized access to Service Provider (In our case it is Salesforce).
You can download certificate by navigating to Axiom application here.
Step 3: Enable Single Sign On in Salesforce
Navigate to “Setup | Security Controls | Single Sign-On Settings” and check “SAML Enabled” option.
Step 4 : Configure Single Sign On
Once SAML is enabled, new section will appear on same page to create New “SAML Single-On Settings”.
Click on New Button and provide following informations
- NAME – any name will work
- API Name – any valid name
- Issuer – Any name. You must remember this as your IDp must pass the same name while sending request
- Identity Provider Certificate – Upload certificate here downloaded on step 2.
- Entity Id – “https://saml.salesforce.com”
- SAML Identity Type – Assertion contains the Federation ID from the User object
- SAML Identity Location – Identity is in the NameIdentifier element of the Subject statement
- Identity Provider Login URL – “http://axiomsso.herokuapp.com/RequestSamlResponse.action” (This URL must be publicly accesible on Internet)
- Service Provider Initiated Request Binding – HTTP POST
Once you are done with settings, you should be able to see seetings page something like this:

Step 5: Generate a SAML Response
Navigate to this URL and click on “generate a SAML Response” link.
Enter following detail in next screen:
- SAML Version – 2.0
- Username OR Federated ID – Once saml is enabled, One new field is created on user record “Federation ID”. This field can be used as a username to validated against IDp. In my case i have provided Employee numver – 123456. Note this is not in Email format.
- User ID Location – Subject
- Issuer – Issuer name which we already in Step4 while configuring SSO. In our case it is AXIOM
- Recipient URL – This should be “Salesforce Login URL” which will be visible once we save SSO settings in Step 4. You can see it in Image 2 above.
- Entity Id – https://saml.salesforce.com
- SSO Start Page – http://axiomsso.herokuapp.com/RequestSamlResponse.action
- User Type – Standard
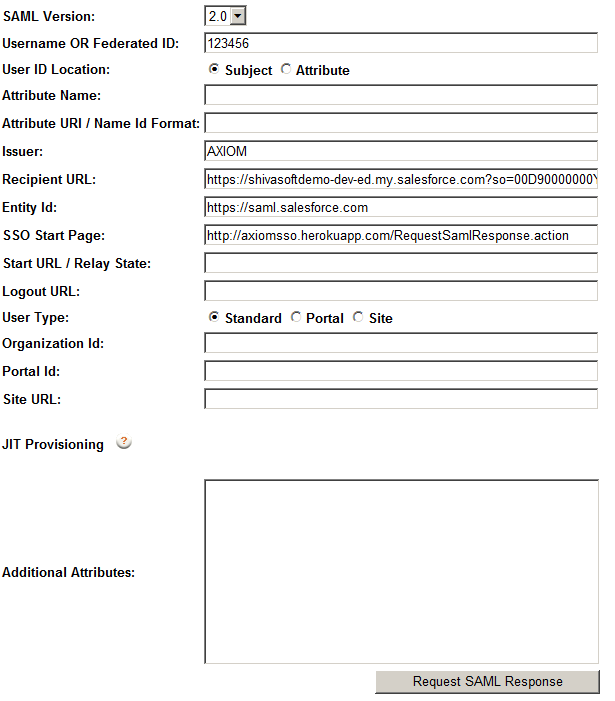
After providing above details click on “Request SAML response” button. Below Screen will appear.

In this page, you can see format of SAML response. You dont have to change anything on this screen, click on Login button.
If everything is OK, you will be on Salesforce Home page.
Question : Can I force users to login with Federated SSO only?
Answer : Yes, Please refer this Article from Salesforce.

Video Tutorial
Leave a Reply