Recently I gave talk in one of most active webinar of Salesforce ecosystem today – Apex hours on topic Integration Patterns and Best Practices in Salesforce.
Response was more than expected and questions were high quality. Therefore, I thought to quickly write high level summary of presentation in this blog post along with Youtube video that you can find towards the end of this post.
Firewall, Proxy and Reverse Proxy
Before integrating anything with Salesforce, as per Architect, it is necessary which system components are important for security and may impact with integration pattern to be used.
Firewalls : It controls and protects Malicious Traffics. Firewall can be hardware or software based.
Proxy aka Forward Proxy : Proxy normally configured in your browser or systems like VsCode, data loader, eclipse to hide your actual identity. Every outgoing request transmits through proxy server to make sure external systems unaware about your true origin and identity
Reverse Proxy : Its used by Web Servers and sits before it. It can server any purpose like authentication or perform security related stuff. Best example is Mulesoft where we can configure API proxy which is used to apply throttling, avoiding DoS attacks or applying SLA as per licenses provided to customer
Factors affecting Integration Patterns
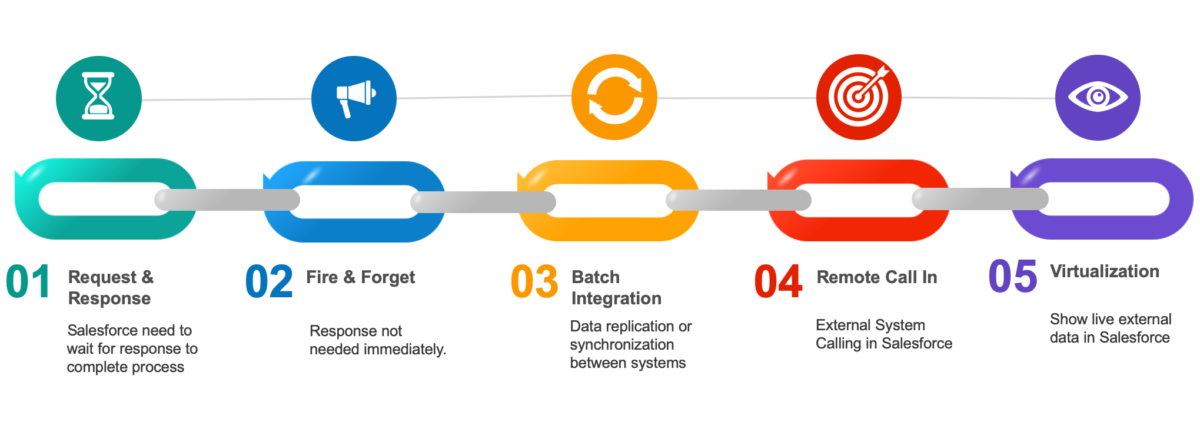
At high level, there are five types of integration patterns in Salesforce
- Request and Reply
- Fire and Forget
- Batch Data Synchronization
- Remote Call In
- Data Virtualization
1. Request and Reply
Few options available in request & reply integration patterns
- External Services
- LWC, Visual force calling external system
- Callouts from Trigger
- Batch Apex invoking external system
2. Fire & Forget



3. Batch Data Synchronization

4. Remote Call-in


5. Data Virtualization
Youtube Video on Salesforce Integration Pattern
Reference
- Mastering Salesforce DX and VSCode
- Platform Event Basics – Trailhead
- Salesforce Documentation on Integration Patterns
- Implementing External Services – Episode 10 of Path to code
- Integrating Salesforce using Rest API – Episode 8 of Path to code




Leave a Reply to JitendraCancel reply